Comprehensive Cyber Security Services
Robust protection for your systems, data, and users, delivered by a trusted cybersecurity company in Nigeria, built to defend against today’s digital threats. Our cybersecurity services ensure network security solutions, data protection services Nigeria, and secure systems that combine IT security, data protection, network security, threat monitoring, and thorough risk assessment.
03
Development Centers
14+
Years Experience
95%
Client Retention
4.8*
Google Rating
Overview
Comprehensive Cybersecurity Service that responds to your business needs
Digital security is more critical than ever. Comprehensive protection safeguards sensitive data, applications, and infrastructure from emerging threats and cyberattacks. From advanced monitoring and encryption to secure network architecture, every layer is designed to strengthen resilience. This approach provides peace of mind and allows businesses to focus on growth without security concerns.
Risk Assessment & Management
Vulnerabilities are identified through detailed evaluations of infrastructure, systems, and processes. Structured risk assessments help prevent threats before they escalate into major incidents. Preventive controls and mitigation strategies reduce exposure to cyber risks. Continuous evaluation ensures long-term protection and compliance.
Network Security Solutions
Network infrastructure is secured through advanced monitoring, firewalls, and intrusion detection systems. Layered defense mechanisms protect against unauthorized access and malicious activity. Proactive monitoring ensures rapid identification of potential threats. A secure network foundation supports stable and uninterrupted operations.
Data Encryption Services
Sensitive information is protected using strong encryption protocols and secure transmission standards. Data remains safeguarded from unauthorized access both in transit and at rest. Encryption strengthens compliance with regulatory requirements. This ensures confidentiality and integrity across digital platforms.
Endpoint Security
Workforce devices are protected against malware, phishing, and unauthorized access. Endpoint monitoring solutions provide visibility across desktops, laptops, and mobile devices. Threat detection systems prevent breaches before they spread across networks. Comprehensive device protection strengthens overall security posture.
CAPABILITIES
The Right Mix of Technologies for Business Success
In today’s competitive environment, speed and performance are essential. Security strategies are designed to enhance operational efficiency while maintaining strong digital protection. Modern tools and frameworks are implemented to safeguard infrastructure without slowing productivity. Specialized expertise ensures the right technologies are aligned with business objectives.
These are some of the platforms and technologies supported:
Cyber Security
Nessus
Cisco ASA
OpenSSL
pfSense
Success Stories
Creating next generation digital products
Enterprise
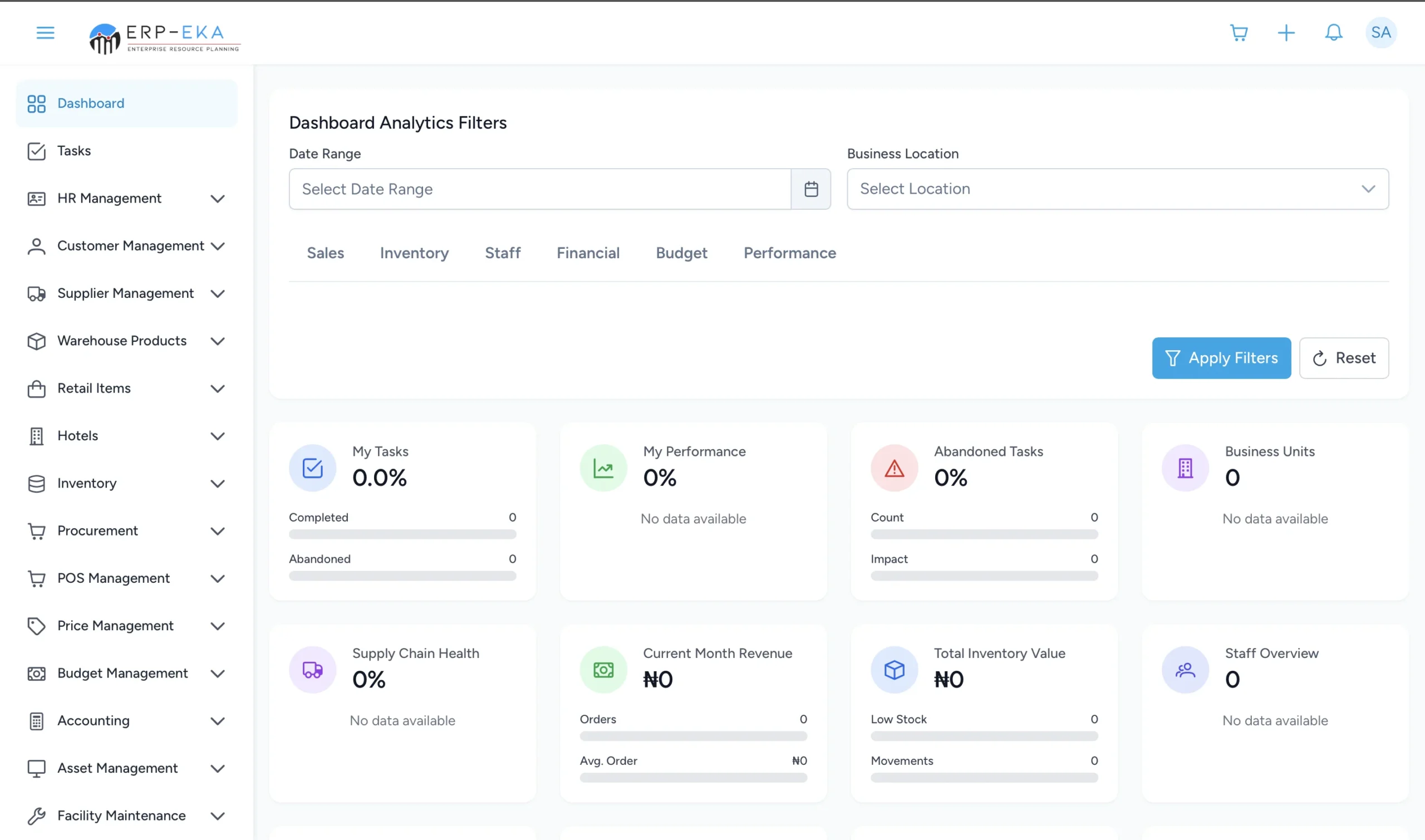
ERP-EKA
ERP Modules Include:
- HR, procurement, POS, inventory, budget, and accounting
- Performance, inventory, and revenue dashboards
- Real-time alerts for stock levels and budget tracking
- Responsive and user-friendly interface
Transportation
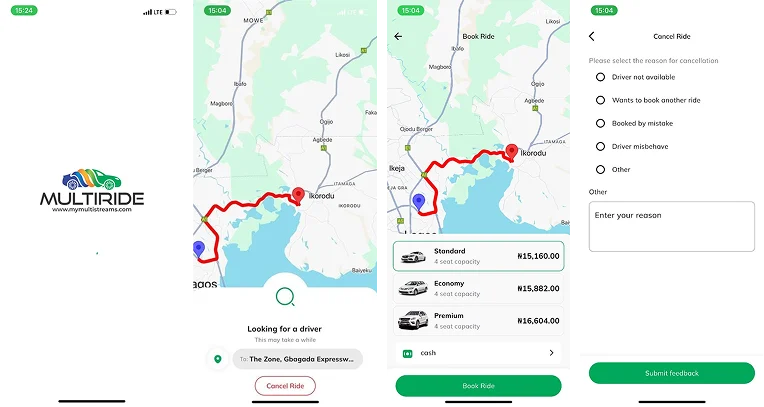
Multiride
Key Features:
- Fast and simple booking
- Affordable fares with clear pricing
- Verified drivers and safety measures
- 24/7 service availability
Manfacturing
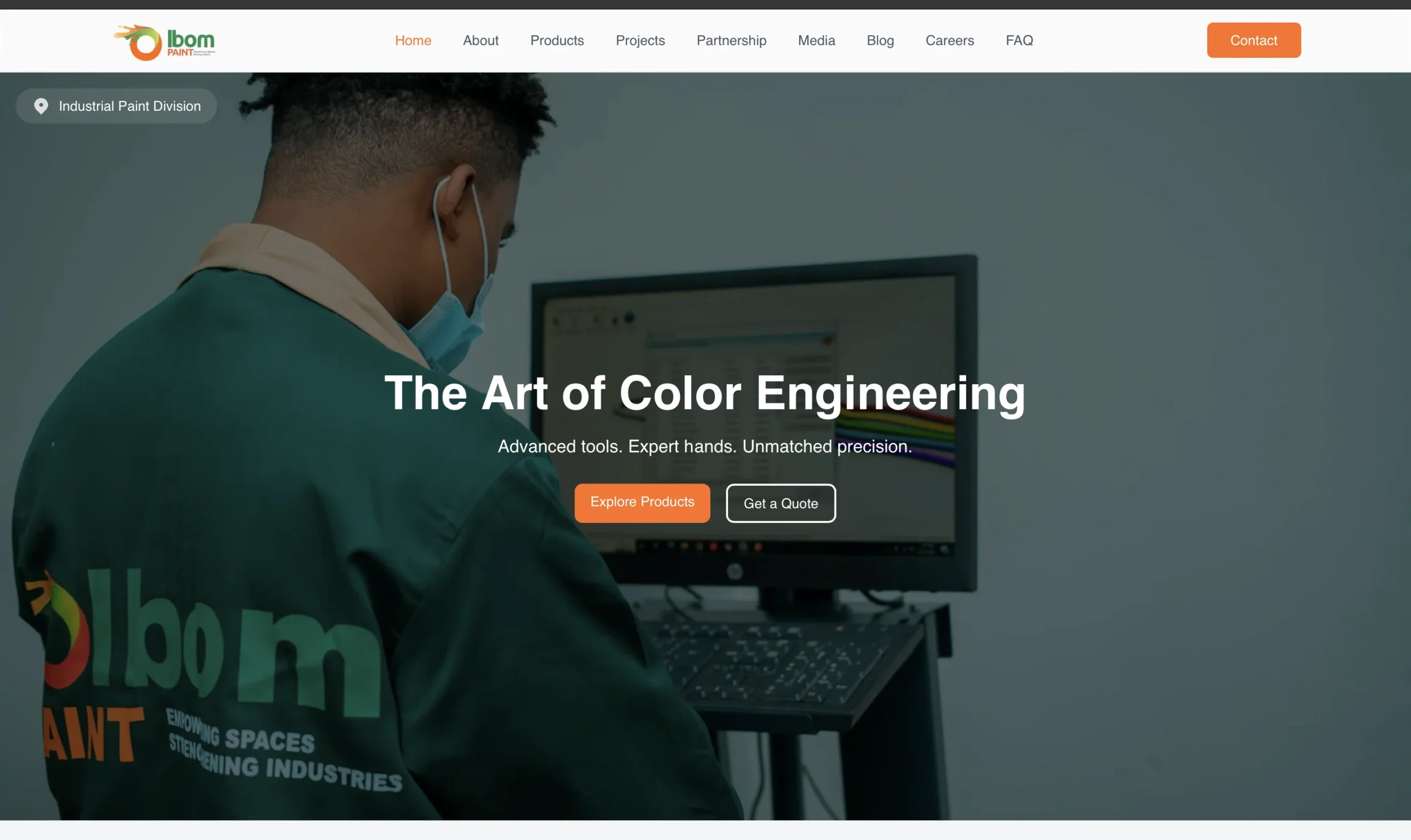
Ibom Paint
Key Features:
- Comprehensive paint catalog and usage details
- Visual showcase of factory operations
- Partnership and career information pages
- Contact and inquiry management tools
Education
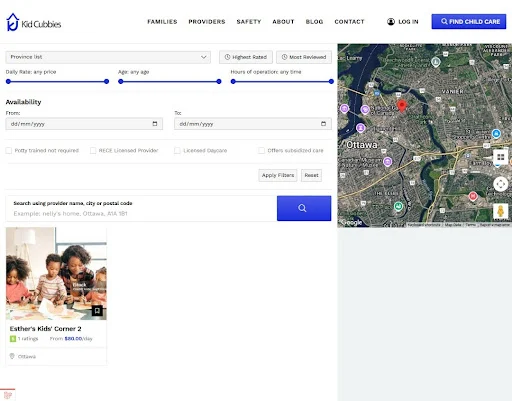
Kid Cubbies
Key Features:
- Verified daycare provider listings
- Search, comparison, and booking tools
- Safety checks and secure messaging
- Administrative insights and analytics
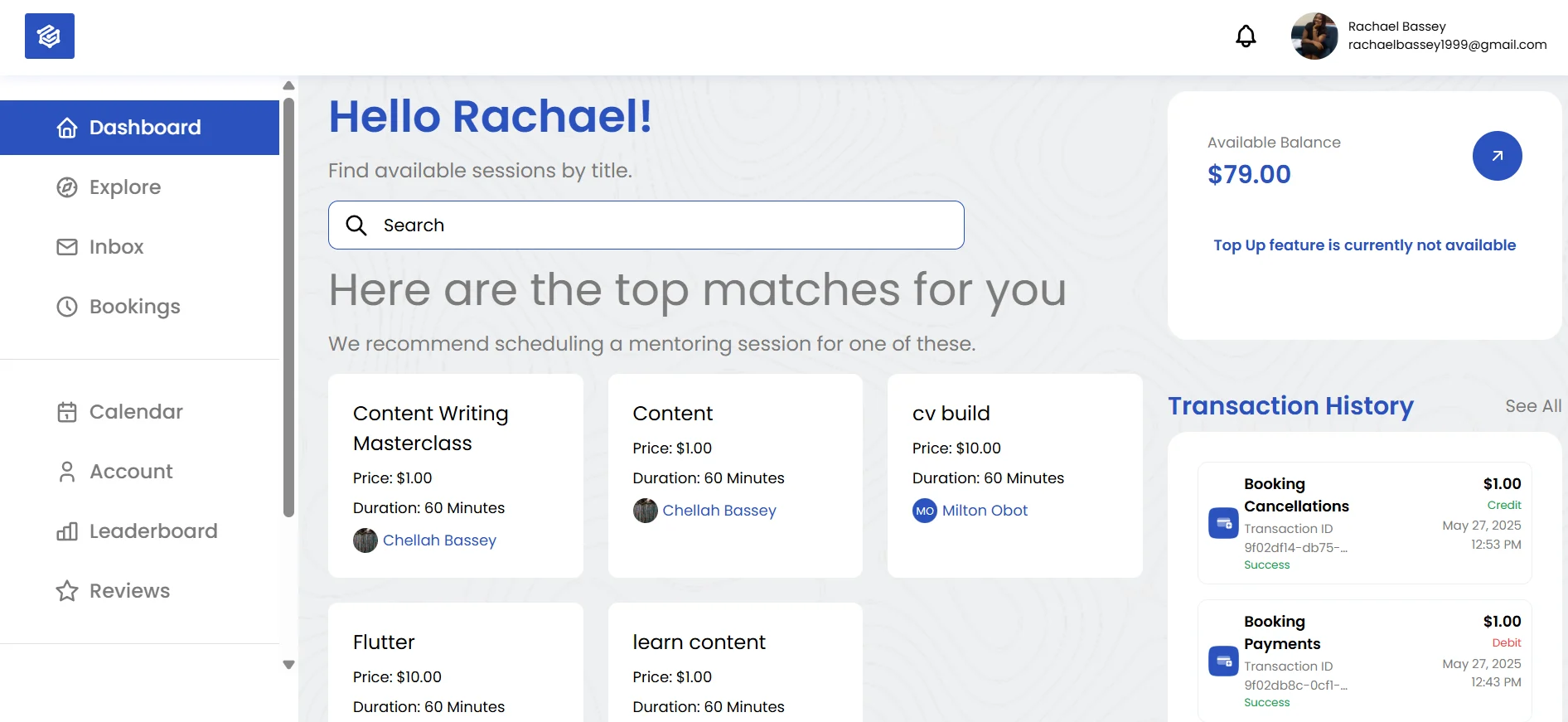
Edutech
Gemsnode
Key Features:
- Personalized dashboard with recommendations
- Mentor search and booking system
- Calendar integration and messaging
- Wallet system and user reviews
TOURISM
Discover Akwa Ibom
Key Features:
- Cultural highlights and event updates
- Vendor registration and management tools
- User-friendly trip planning interface

PROCESS
A Structured Approach to Delivering Secure Digital Environments
A methodical framework guides every project from initial assessment to long-term monitoring. Each phase ensures alignment with business goals while minimizing security risks. Clear documentation and collaboration remain central throughout implementation. This structured process delivers dependable and measurable protection.
Requirement Analysis
Existing infrastructure is assessed to identify vulnerabilities and define security objectives. Threat landscapes and compliance requirements are carefully evaluated. Findings are documented to create a clear security baseline. This phase establishes the foundation for a tailored protection strategy.
What You Get
- Risk & threat assessment
- Security requirements documentation
- Time and cost estimate
- NDA and IP protection
Strategy & Planning
A customized cybersecurity roadmap is developed based on identified risks and operational needs. Security architecture, protocols, and compliance measures are clearly defined. Policies and response frameworks are aligned with regulatory standards. Detailed planning ensures scalable and sustainable protection.
What You Get
- Security architecture design
- Compliance & policy alignment
- Incident response plan
- Project scope and timeline
Implementation & Hardening
Security tools such as firewalls, encryption systems, and endpoint protection are deployed and configured. Network and application hardening reduces vulnerabilities across environments. Access controls are strengthened to prevent unauthorized activity. Continuous risk mitigation ensures systems remain secure.
What You Get
- Security tools configuration
- Network and application hardening
- Access control and encryption protocols
- Ongoing risk mitigation
Monitoring & Support
Threat monitoring systems operate continuously to detect and respond to potential incidents. Regular updates and patching maintain defense against evolving risks. Incident response mechanisms minimize downtime and disruption. Ongoing support ensures stability, visibility, and long-term resilience.
What You Get
- Real-time threat monitoring
- Incident detection & response
- Regular updates and patch management
- 24/7 support and reporting
WHY TEDIKOM WIRELESS?
We Focus on the Core Elements of Excellence
With extensive industry experience, we understand that successful digital products must be secure, scalable, and user-friendly. Our commitment to quality ensures every solution meets high performance standards. We prioritize long-term sustainability in every system we build. These core principles guide our execution across all projects.
Security First – Every solution is protected with advanced cybersecurity measures and proactive monitoring. We implement encryption and industry-standard protocols to safeguard sensitive data. Risk mitigation strategies are integrated throughout development. This ensures a secure and resilient digital environment.
User-Centered Design – We design intuitive interfaces that prioritize clarity and accessibility. Each interaction is structured to enhance usability and engagement. Our focus is on creating seamless digital experiences. This approach improves satisfaction for both customers and internal teams.
Scalability & Performance – Our systems are engineered to handle growth without compromising speed or stability. Infrastructure is designed to support high traffic and large data volumes. Performance optimization is integrated into every layer of development. This ensures reliability as your business expands.
AI-Powered Efficiency – We integrate automation and intelligent tools to streamline workflows. AI-driven insights support better operational decisions. Smart systems reduce repetitive tasks and improve productivity. This enables businesses to operate more efficiently.
Data-Driven Strategies – We leverage analytics and real-time tracking to guide strategic decisions. Performance metrics provide visibility into operational effectiveness. Data insights help refine processes and improve outcomes. This ensures informed and measurable growth.
Seamless Integration – Our solutions connect effortlessly with existing systems and third-party platforms. Integration is planned carefully to avoid disruption. We ensure compatibility across cloud and enterprise environments. This results in smooth transitions and improved productivity.
ENGAGEMENT MODELS
Flexible Solutions Tailored to Your Business Needs
Behind every great solution is a clear understanding of people and process. Our engagement models are built to support both—seamlessly.
DEDICATED RESOURCES
For businesses requiring consistent development support, we provide dedicated teams that function as an extension of your organization. This model ensures focused attention and continuous collaboration. Our specialists integrate seamlessly with your internal processes. The structure allows flexibility as project needs evolve.
RECOMMENDED FOR
- Full-time development specialists
- Close collaboration with in-house teams
- Agile iterations and rapid updates
- Scalable resource allocation
PROJECT-BASED MODEL
Ideal for organizations with clearly defined objectives, this model delivers end-to-end execution within an agreed scope, budget, and timeline. A structured framework ensures accountability and measurable progress. Dedicated professionals focus solely on achieving defined deliverables. This approach provides clarity, predictability, and high-quality outcomes.
PROJECT-BASED MODEL
- Clearly defined digital projects
- Fixed budgets and timelines
- Startups and established enterprises
- Custom technology initiatives
Words Of Appreciation
Voices Of Trust And Confidence
Meet our Tech Partners



What Happens Next?
You’re one step closer to bringing your dream product to life. Here’s how the process unfolds:
- Send Your Request. Tell us what you need.
- We Contact You. We’ll discuss your goals.
- Get a Proposal. You’ll receive a plan and quote
- We Begin. Work starts after your approval.
Tedikom specializes in custom software development, IT consulting, cloud computing, cybersecurity, AI-driven solutions, business process automation, and enterprise solutions to help businesses scale efficiently.
Tedikom provides solutions for various industries, including finance, healthcare, education, e-commerce, logistics, manufacturing, and startups. Each solution is tailored to the specific challenges and needs of the industry.
Yes! Tedikom builds custom mobile and web applications designed for scalability, security, and a seamless user experience. Whether it's an e-commerce platform, SaaS product, or enterprise application, Tedikom ensures high-performance solutions.
To get started, simply contact Tedikom via their website, email, or phone to schedule a consultation. Their team will assess your needs, propose a tailored solution, and guide you through the development process to ensure a successful digital transformation.
Browse Other Offerings from Tedikom Wireless
Discover more of our solutions and services designed to empower your business
Other Solutions
Other Services